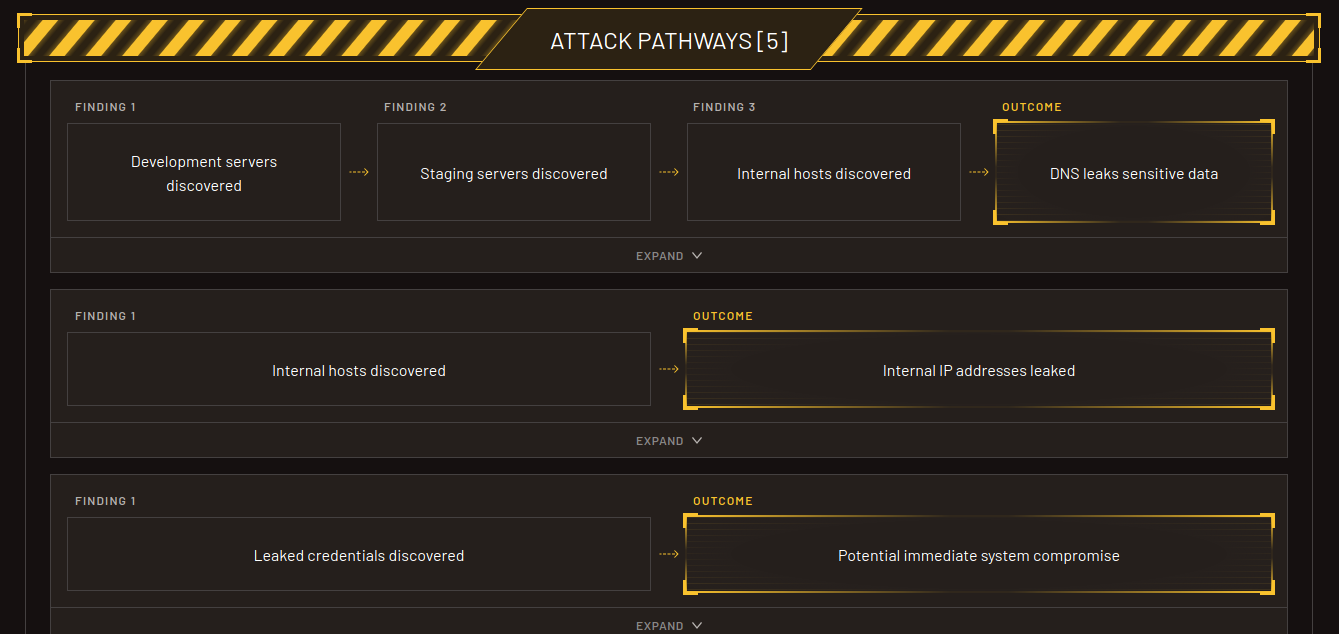
Phobos Orbital is designed to illustrate where real attackers would attack, and why. Orbital will discover Attack Pathways which make quick work of exposed risk surfaces, indicating the most lucrative entrypoints available for exploitation.
700 page reports with 4 column wide CVE references don't help when solving real security problems - showing you where attackers would go first, with plain-language reporting does.
Attack Pathways(tm) are a novel technique to describe how a series of informational, low and medium tier findings can be chained together to form criticals and highs! Orbital produces these programatically based on the findings in every report! Attack Pathways(tm) provide the perfect avenue to gauge at a glance how findings every other scanning platform ignores or makes light of can be leveraged by attackers in ways ignored completely by contemporary scanning platforms, and compliance frameworks.
No CVE references, no DREAD, no STRIDE, no att&ck framework - plain english. Instantly actionable reports you can share with anyone. The days of multi-hundred page reports consisting of the same copypasted "ping is a medium finding" and "here's how to fix XSS and SQLI" are over.
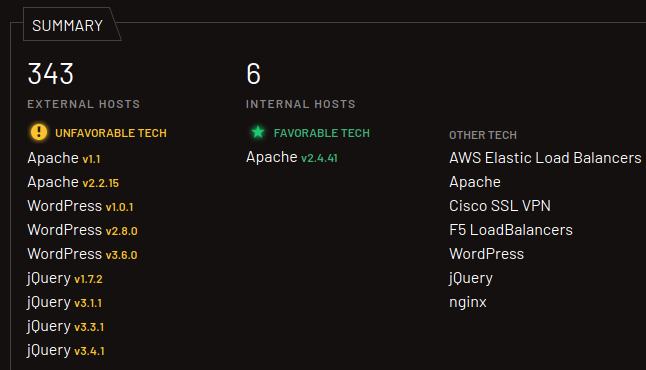
Identify the Tech Stack of a given organization. Often just looking at the technology used telegraphs quite a lot to attackers. Multiple security appliance providers have had multiple RCE problems in the last 2-3 years. Clawedbot is a thing now, npm apps, s3 buckets and other tooling expose sensitive files leading to breaches every day!
Get an idea of what a given host is responsible for based on its DNS names. Internal IP? Dev and Staging language in it's name? Probably a soft target, probably not hardened. Attackers look for easy ways in, and this is how they do it. Who sends dev/stage/qa logs to the SIEM? It's too much noise! Attackers know that, and it's where they strike.
Orbital gets straight to the meat.
Discover what other domain names and organizations are adjacent to your inquiry! Orbital can show you how organizations can overlap at the technology level, giving way for attackers to have multiple avenues of attack.
Identify “juicy targets”: publicly accessible assets, leaks, appliances/software with known issues, and combined findings for attacker success. At the end of the day, the decision tends to be "go" or "no go", and by classifying assets into favorable or unfavorable, we help make the decision process easy!
Visually verify what’s exposed and what changed, fast. In many cases, just seeing the screenshot of what has been exposed is enough to make a decision.
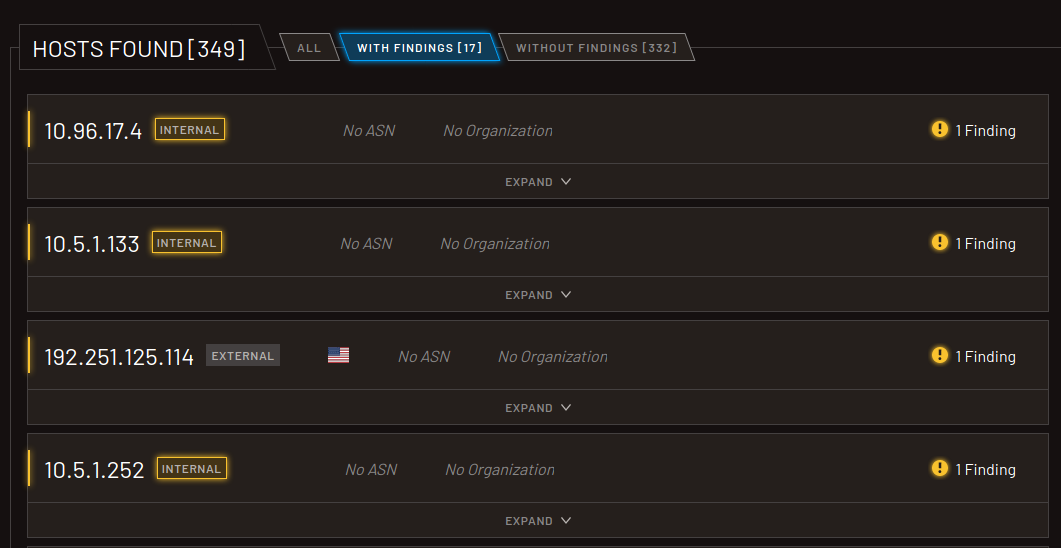
Orbital can discover internal assets using only publicly available data. See what leaks “behind the curtain” and how attackers use it for intel.
In many cases, host firewalls or cloud dashboards can be a pain, and are easy to misconfigure. Findings like these are easily spotted with Orbital!
Gold for attackers. Orbital surfaces exposed credentials to identify likely ingress opportunities.
One page. Plain english. Looking at the executive report for 60 seconds will show you more about your environment than looking at a 600 page report full of corporate fluff for any amount of time (plus your eyes dont bleed!)
Orbital’s sweeps are exhaustive, and often turn up findings nobody knew existed. We only display real findings, no fluff, padding, or repeating the same text over and over again to pad the report.
Click any image to zoom.
Orbital is is a straightforward way to handle external inventory + continuous perimeter monitoring + audit-friendly evidence. Where a framework requires a specific scan vendor (ex: PCI ASV), Orbital is the “make sure nothing surprises you” layer.


Billing options available: Monthly, Quarterly or Anually.
Once you sign up for a trial and run your first report, you'll know how many hosts Orbital found, and which pricing tier will be assigned!
Orbital can help you get a 100,000 foot view of your organizational perimeter, be it in the cloud, on premise, or across various hosting and technology providers. See what attackers see, and tune your risk surfaces!